An often overlooked aspect of benchmarking is its use to develop security staffing levels for new facilities. When facilities are built or redeveloped, most of the focus is on the design and construction implementation and other aspects of the occupancy process such as office layouts, furniture, inspections, close outs, and move in. On many such projects, staffing plans to secure the facility are an afterthought. Security contractors have been known to take advantage of this situation and offer security pricing that is non-competitive as the building transitions from the contractor to the owner.
Data entered in a benchmarking system can be used to determine staffing levels for security operations. While security services are a smaller percentage of the operating expenses than maintenance and utilities, they still represent a significant expense on an annual basis and over the building life. For the building life, operating costs typically represent more than 90% of the life-cycle costs and the appropriate staffing levels have a significant impact on the overall security of the facility. Using benchmarking is a straightforward process that shows the importance of the FM position in the organization and the impact of staffing decisions over the life-cycle of the building. Without good benchmarking comparisons, you may not realize:
- Staffing levels may need to be increased or decreased.
- Your level of service is too low.
- Which best practices may have the most impact on improving the staff utilization.
As you can see, a case can be easily made for benchmarking that will justify the minor amount of staff time. We have used examples from FM BENCHMARKING to illustrate how easy the process should be. This approach will allow you obtain the key output reports in minimal time. In the following example we benchmarked an office facility for security staffing levels.
For a quick analysis, of a 400,000 GSF building that is under construction we can utilize FM BENCHMARKING LITE to create a chart showing the area cleaned per full time security worker.
Comparing your security staffing levels may give you the wrong perspective on your performance unless the comparisons are made with a relevant peer group. We initially define our peer group to be office buildings of a similar size to our own building.
For security staffing the chart below shows a wide range across all quartiles of about 15,000 securable square feet overseen per FTE security worker.
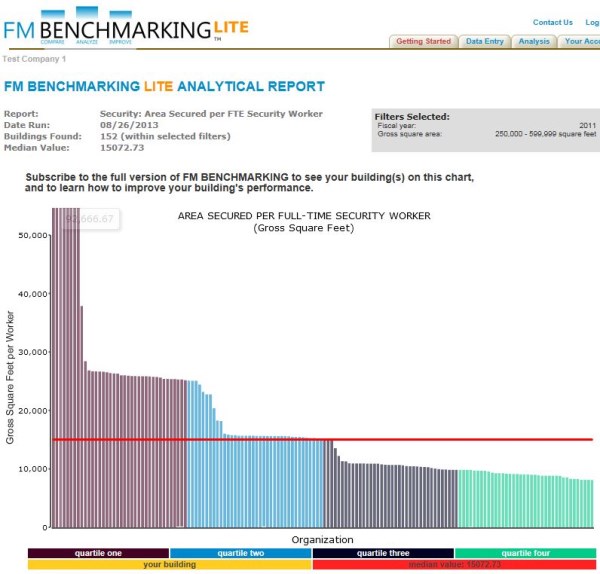
Filters: Type of facility (Office) Size 250,000 — 599,999 sq. ft.
Most FMs probably would prefer to staff up the security organization over time. A security staffing plan appropriate for most organizations is one that initially moves into the facility with minimum staff and then increases staff if needed. A prudent staffing plan would be to utilize the first quartile value, say around 25,000 square feet overseen per FTE security worker and then increase the staffing a bit if more security is needed. Using benchmarking data in this way provides a rational and easily defended approach to developing a staffing plan.
Now suppose your facility operates 24 hours per day. You would expect the staffing needs would be greater and comparative data would look different. Here is the chart with an added filter of 19-24 hours per day of operation (because we turned on an additional filter, there our less buildings in our filter set).
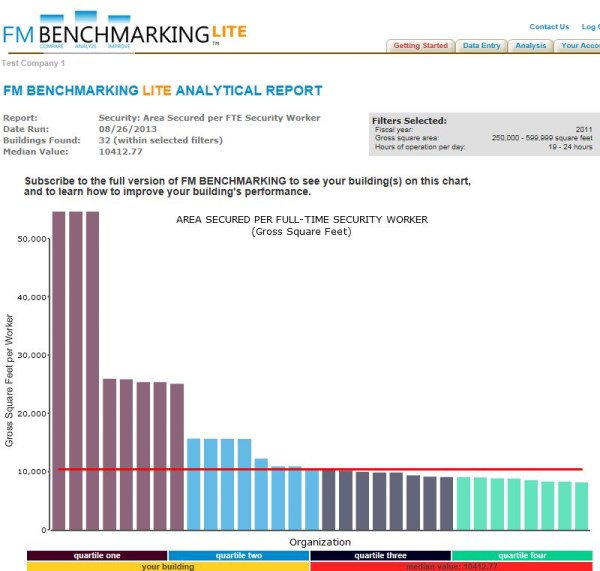
Filters: Type of facility (Office) Size 250,000 — 599,999 sq. ft. and 19-24 hours of operation per day
Note that the median has dropped from 15,000 gsf per FTE security worker to about 10,000 gsf per FTE security worker. Clearly the hours of operation have a significant impact on the staffing requirements.
The case can be made to focus our efforts on implementing the key aspects that will influence the overall security operating costs and improve the efficiency of the staff. Security services are compared on a cost per area basis. This type of analysis doesn’t show you how to improve your performance through best practices, but it does give you an idea of how your peer group is performing. To see what needs to be done to improve performance, you will need to benchmark the best practices, which is a different type of analysis requiring additional tools. Several other papers in this section show such examples.